Tested & Proven Effective
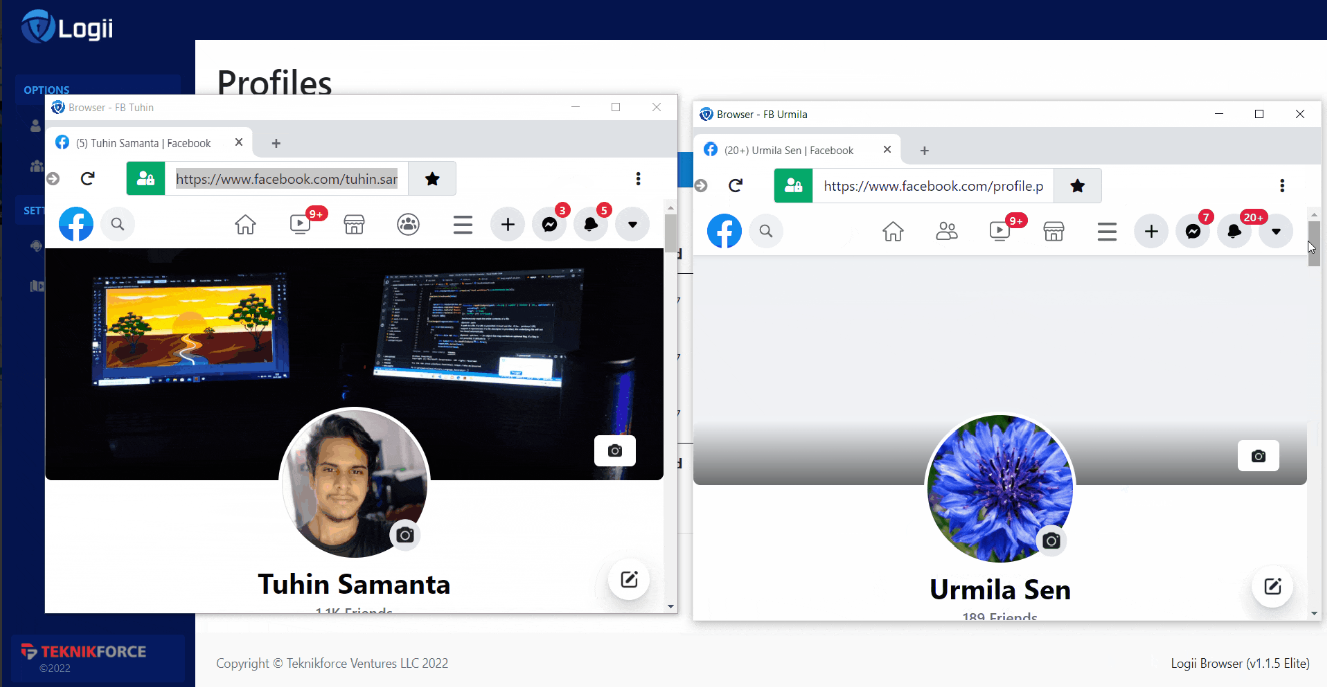
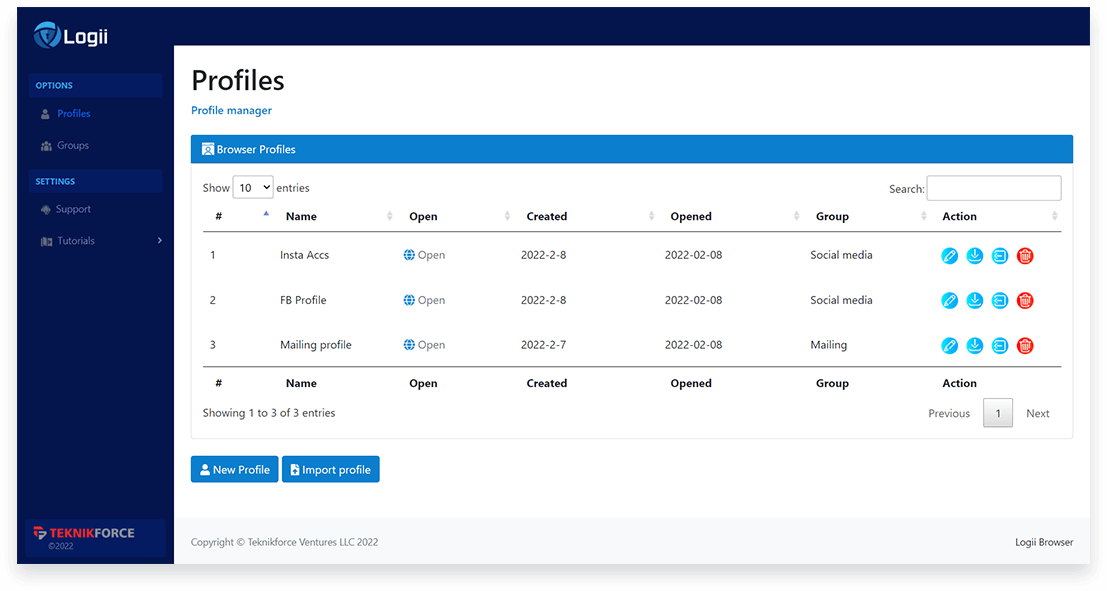
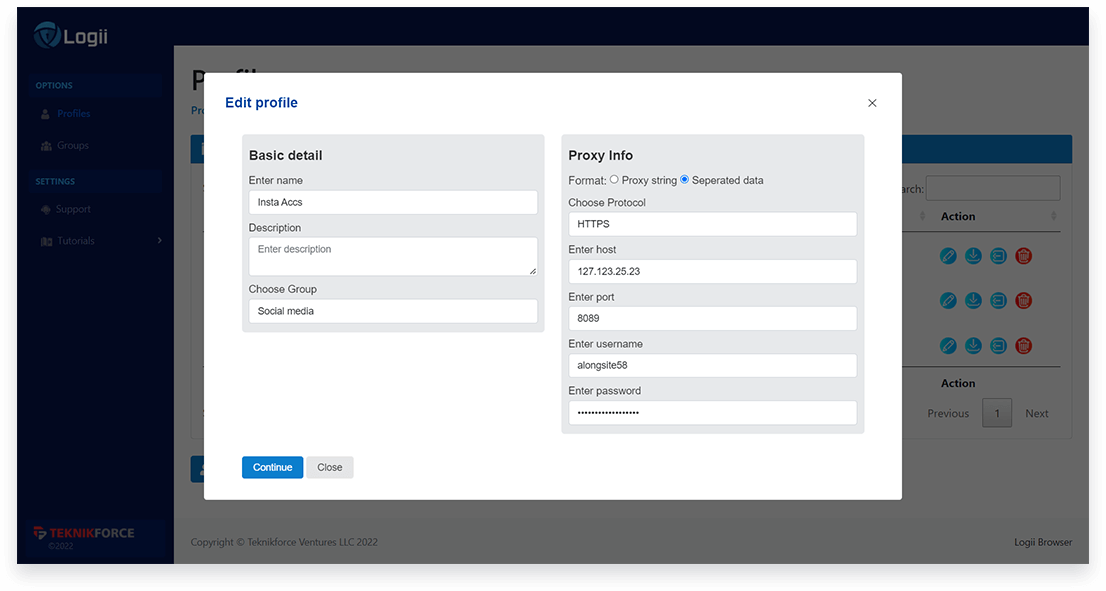
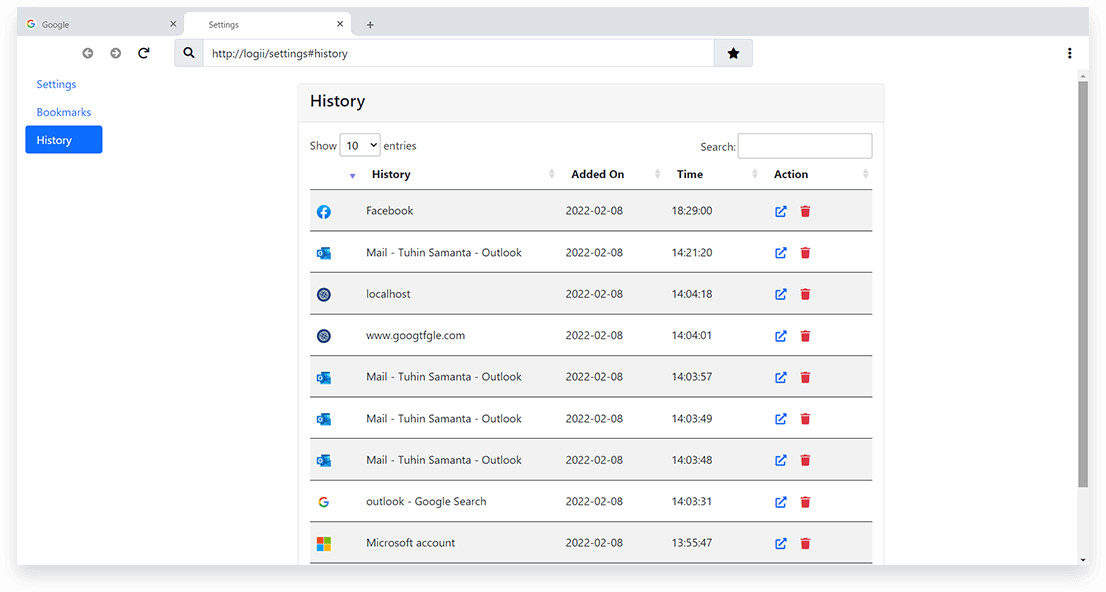
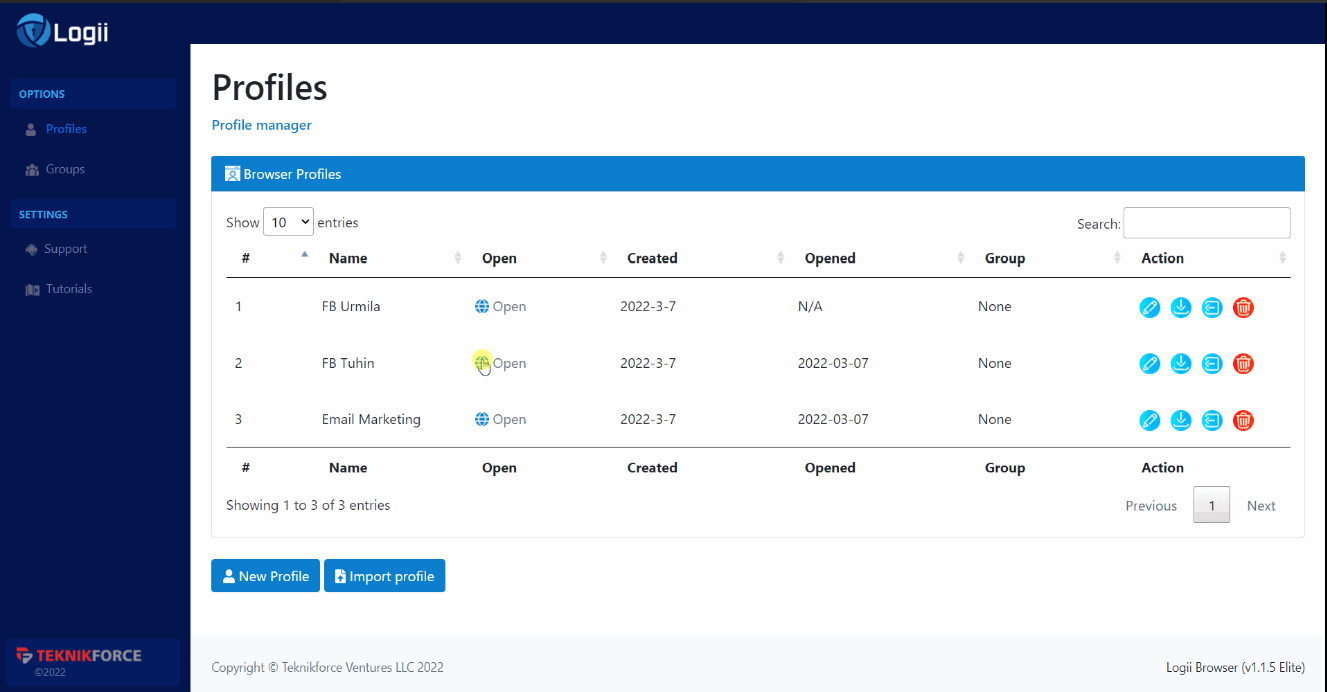
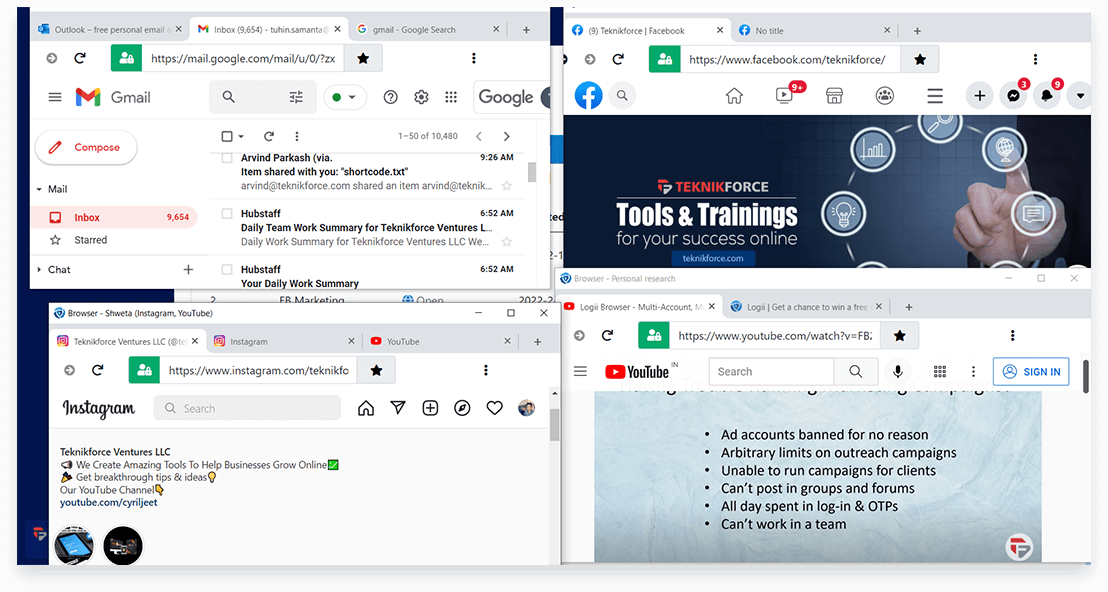
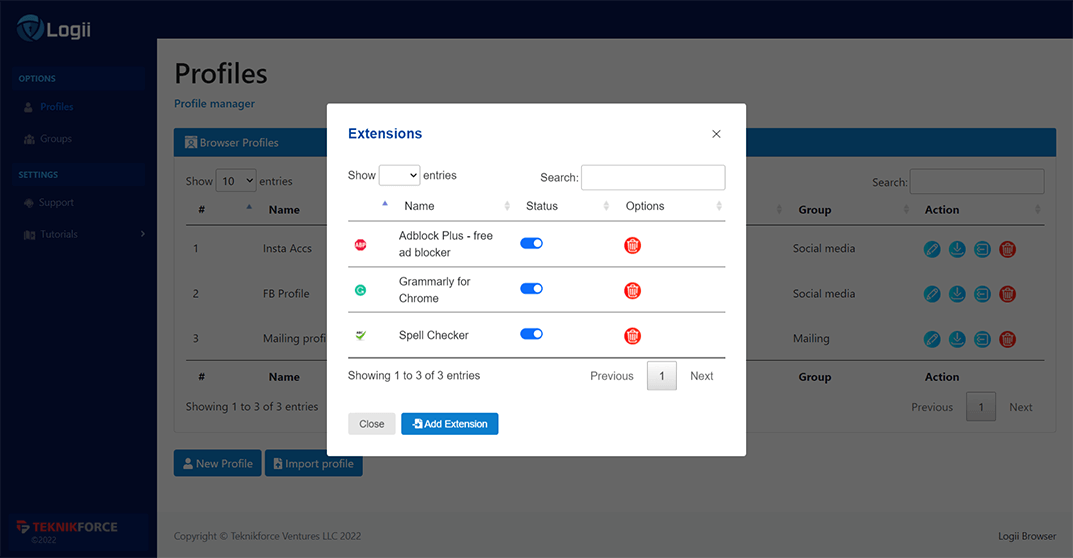
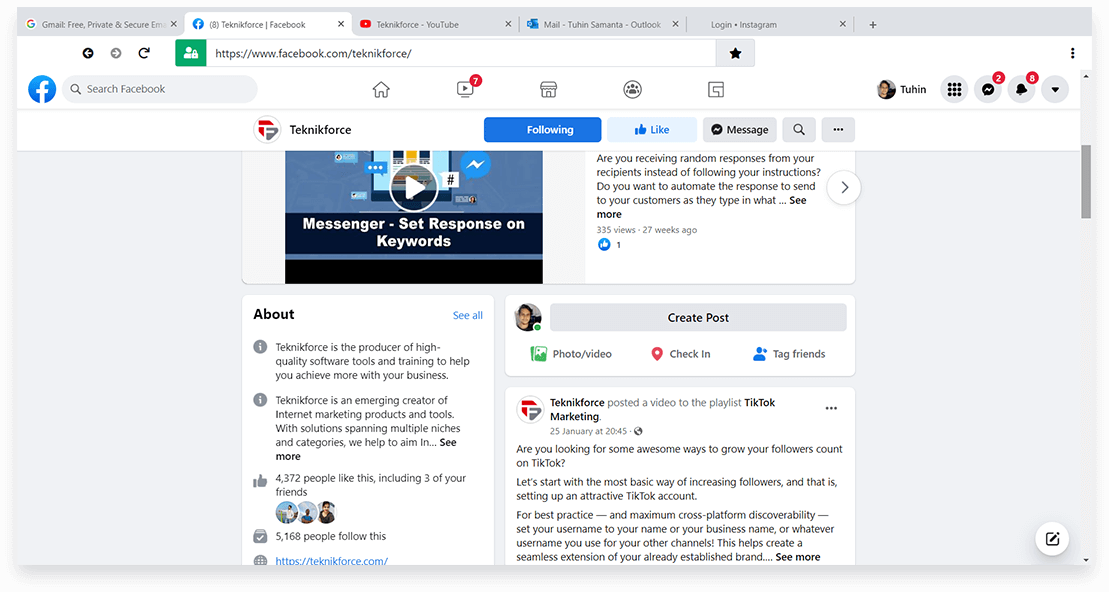
Multiple Marketers Use Logii To
Run Their Ad Accounts & Social
Media Marketing Campaigns
Successfully
In closed-group testing with our
existing beta customers & associates















 AdsPower
AdsPower Multilogin
Multilogin GoLogin
GoLogin